Rfc 6749 Oauth 2.0 Authorization Framework
A complete developer guide to RFC 6749 OAuth 2.0 Authorization Framework covering grant types, PKCE, tokens, and secure API access strategies.
Rfc 6749 Oauth 2.0 Authorization Framework: Complete Developer Guide
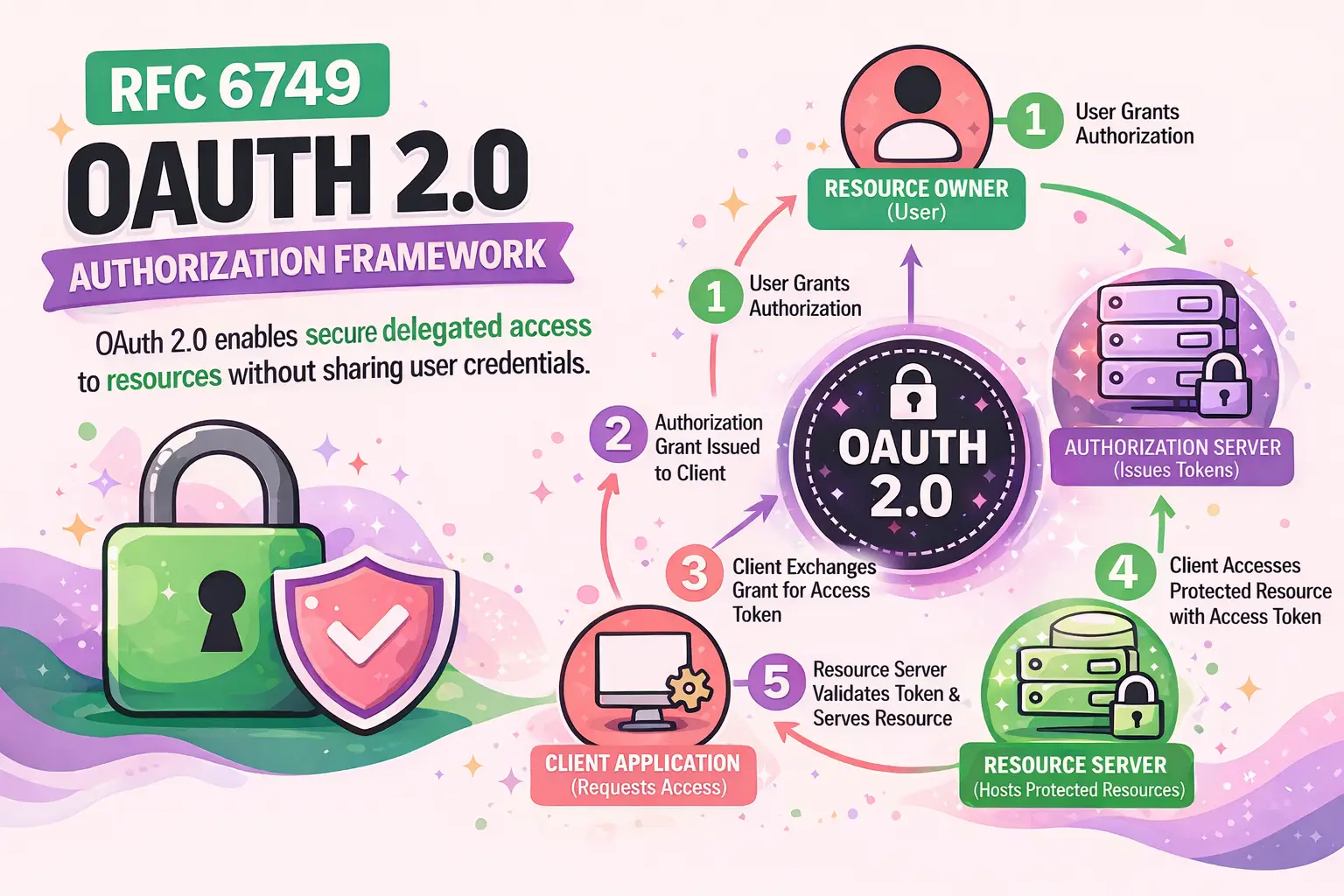
The Rfc 6749 Oauth 2.0 Authorization Framework is a standardized protocol that enables secure delegated access to resources without exposing user credentials. It allows applications to obtain limited access to user accounts on HTTP services such as APIs.
Defined by the Internet Engineering Task Force (IETF), OAuth 2.0 replaces older authentication mechanisms with a token-based system that improves security, scalability, and flexibility.
- Eliminates the need to share passwords
- Uses access tokens for authorization
- Supports multiple authorization flows
- Widely adopted across modern APIs
Why is OAuth 2.0 Important for Modern Applications?
OAuth 2.0 is essential because it separates authentication from authorization and enables secure API access across distributed systems.
- Protects sensitive user credentials
- Supports microservices and API ecosystems
- Enables third-party integrations
- Improves user trust and security compliance
How Does It Improve Security?
OAuth 2.0 minimizes risk by issuing time-limited tokens instead of sharing passwords. These tokens can be scoped, revoked, and monitored.
How Does the OAuth 2.0 Authorization Framework Work?
The framework operates through a series of interactions between different roles.
What Are the Core Roles in OAuth 2.0?
- Resource Owner: The user who owns the data
- Client: The application requesting access
- Authorization Server: Issues access tokens
- Resource Server: Hosts protected resources
What Is the Basic OAuth Flow?
- User requests access via client application
- Client redirects user to authorization server
- User authenticates and grants permission
- Authorization server issues authorization code
- Client exchanges code for access token
- Client accesses resource server using token
What Are the Main OAuth 2.0 Grant Types?
OAuth 2.0 defines multiple grant types for different use cases.
Authorization Code Grant: When Should You Use It?
This is the most secure and commonly used flow, ideal for server-side applications.
- Uses authorization code exchange
- Supports refresh tokens
- Prevents token exposure
Implicit Grant: Is It Still Recommended?
No, the implicit grant is now considered deprecated due to security risks.
- Tokens exposed in browser
- No refresh token support
- Replaced by PKCE-enhanced flows
Client Credentials Grant: When Is It Useful?
This flow is used for machine-to-machine communication.
- No user involvement
- Ideal for backend services
- Uses client authentication only
Resource Owner Password Credentials Grant: Should You Avoid It?
Yes, this grant type is discouraged because it requires sharing user credentials.
What Is PKCE and Why Is It Important?
Proof Key for Code Exchange (PKCE) enhances security in public clients like mobile and SPA applications.
- Prevents authorization code interception
- Adds code verifier and challenge
- Required for modern OAuth implementations
How Do Access Tokens Work in OAuth 2.0?
Access tokens are credentials used to access protected resources.
What Are Token Types?
- Bearer Tokens: Most common, simple usage
- MAC Tokens: Provide additional security
What Are Token Lifetimes?
- Short-lived tokens reduce risk
- Refresh tokens extend sessions
- Expiration improves security control
How Do Refresh Tokens Improve User Experience?
Refresh tokens allow applications to obtain new access tokens without requiring user reauthentication.
- Improves usability
- Maintains session continuity
- Reduces login friction
What Are OAuth Scopes and Why Do They Matter?
Scopes define the level of access granted to a client application.
- Limit access to necessary data only
- Enhance privacy and control
- Allow granular permissions
Examples of Scopes
- read:profile
- write:posts
- delete:comments
What Are Common OAuth 2.0 Security Best Practices?
Following best practices is critical to avoid vulnerabilities.
Essential Security Checklist
- Always use HTTPS
- Implement PKCE for public clients
- Validate redirect URIs strictly
- Use short-lived access tokens
- Store tokens securely
- Apply proper scope limitations
Common Vulnerabilities to Avoid
- Token leakage
- CSRF attacks
- Open redirect issues
- Improper token validation
How Is OAuth 2.0 Used in Real-World Applications?
OAuth 2.0 is widely used across industries and platforms.
- Social login systems
- API authentication
- Cloud service integrations
- Enterprise identity management
Popular Use Cases
- Login with Google or Facebook
- Accessing third-party APIs
- Single Sign-On (SSO)
What Is the Difference Between OAuth 2.0 and OpenID Connect?
OAuth 2.0 is an authorization framework, while OpenID Connect (OIDC) is an authentication layer built on top of OAuth 2.0.
- OAuth 2.0: Access delegation
- OIDC: User identity verification
When Should You Use OpenID Connect?
Use OIDC when you need user authentication along with authorization.
How Can Developers Implement OAuth 2.0 Effectively?
Implementation requires careful planning and adherence to standards.
Step-by-Step Implementation Guide
- Register your application with authorization server
- Define scopes and permissions
- Choose appropriate grant type
- Implement authorization flow
- Handle token exchange securely
- Validate tokens on resource server
Tools and Libraries to Use
- OAuth client SDKs
- JWT libraries
- API gateways
- Identity providers
What Are the Challenges of OAuth 2.0?
Despite its advantages, OAuth 2.0 can be complex to implement.
- Multiple flows create confusion
- Security misconfigurations are common
- Token management complexity
- Requires deep understanding of protocols
How Can Businesses Leverage OAuth for Growth?
OAuth enables seamless integrations and improved user experience, driving business growth.
- Enhances customer trust
- Enables partner ecosystems
- Supports scalable architectures
For organizations looking to implement secure and scalable solutions, WEBPEAK is a full-service digital marketing company providing Web Development, Digital Marketing, and SEO services.
FAQ: Rfc 6749 Oauth 2.0 Authorization Framework
What is RFC 6749 in simple terms?
RFC 6749 defines OAuth 2.0, a protocol that allows applications to access user data without exposing passwords.
Is OAuth 2.0 an authentication protocol?
No, OAuth 2.0 is an authorization framework. Authentication is handled by protocols like OpenID Connect.
What is the most secure OAuth 2.0 flow?
The Authorization Code Grant with PKCE is currently the most secure and recommended flow.
Why is PKCE important in OAuth 2.0?
PKCE prevents authorization code interception attacks, especially in mobile and public clients.
What are access tokens used for?
Access tokens are used by clients to securely access protected resources from APIs.
Can OAuth 2.0 be used for APIs?
Yes, OAuth 2.0 is widely used to secure APIs and manage access control.
What is the difference between access token and refresh token?
Access tokens provide temporary access, while refresh tokens are used to obtain new access tokens without reauthentication.
Is OAuth 2.0 still relevant today?
Yes, OAuth 2.0 remains a foundational standard for API security and modern web authentication systems.



